Phylum Launches Ruby, Python, and new UI/UX
We recently launched a major redesign of the product and rolled out new languages, including Ruby and Python.
Read on for more detail about these exciting new updates that are now integrated into Phylum and see what’s ahead on the product roadmap!
New Features & Languages
Expanded Language Support - In addition to Javascript and Typescript, we now support Ruby and Python. More languages are coming soon!
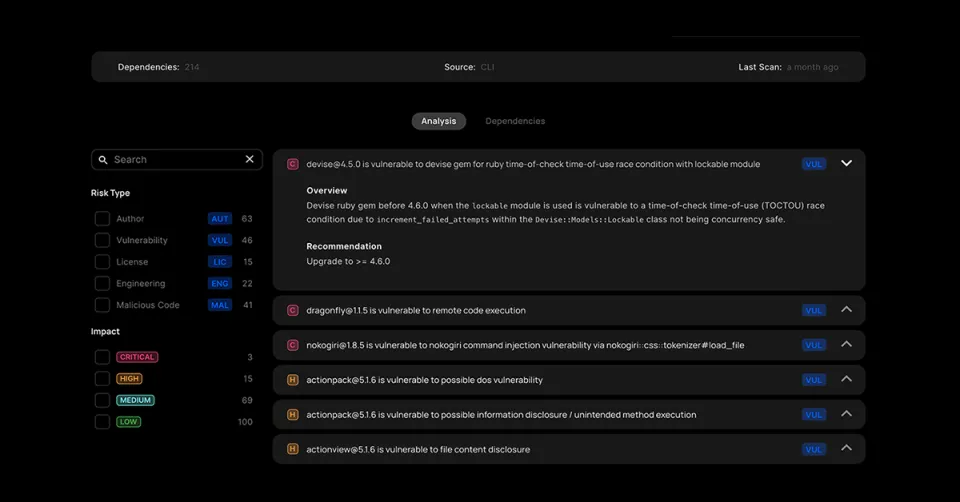
Web User-Interface Launched - It’s stunning and easy-to-use. The new WebUI greatly increases our API-first reporting capabilities. Check it out here.
Self-Update Functionality - In addition to major UX improvements to our command-line interface (CLI) tool, we added a secure update capability. Phylum's CLI uses minisign for signature verification to ensure that our software supply chain protection system is strengthened and protected from software supply chain issues.
MacOS CLI Release Binaries - Our open-source CLI tool now generates release binaries for MacOS in addition to Linux. Windows is supported but requires building the binary from source.
Additional Improvements
Scoring - We take the design of risk scoring very seriously and made some further improvements to ensure that Phylum’s open-source risk score is meaningful, actionable and that it will function properly across vast swaths of software. More detail can be seen here.
CLI UX - We completely overhauled the user experience provided by the command-line tool to make it incredibly easy to use.
Backend Package Processing Speed - We made significant speed enhancements to ensure that we can operate at the speed of modern development and match the pace of open-source developers.
Data Access Speed - We improved the performance of our data management system so that both CLI and Web interfaces are responsive and our CI/CD integrations are performant.
Issue Descriptions - We made substantial updates to provide issue feedback on open-source packages that are useful, understandable, and actionable to users.
New Analytics Released
New analytics that help identify significant risks in the open-source ecosystem include:
Anomalous Author Activity Detection - We have a new analytic to identify possible bad behavior in conjunction with evidence from other analytics and models.
Pre- and Post- Install Hook Analysis - We leverage our static analysis capability to identify dangerous uses of pre and post install functionality in package managers.
What’s next?
More Languages - Java and many more languages will be supported soon.
Rules Engine - There are few cases where a single indicator will correlate to a critical security issue. Frequently, you need to consider multiple risk indicators simultaneously to properly identify issues in the software supply chain. The rules engine will enable these types of complex analyses, improve scoring and issue accuracy, and maintain a high signal-to-noise ratio amidst the undercurrent of constantly changing open-source software.
Static Analysis Improvements - We continue to improve our static analysis system to identify more indicators of supply chain risk. Look for an upcoming blog article that goes deeper into how we are accomplishing this goal.
Developer Tools Analysis - Developer tools are a rapidly expanding area completely underserved by defensive tools. Applying our unique approach to software supply chain risk analysis will enable us to properly defend developer tools.
Dynamic Analysis - We are adding a dynamic analysis capability to our processing pipeline to augment our static analysis system.
Query API - Our upcoming query API will enable users to author their own analytics and identify new and novel issues using our platform.




